Recent Posts
The Myth: Controller Area Network is “Too Easy to Hack”
Posted by on

The potential security issues of CAN and its higher-layer protocols attract increased attention from the automotive, control, and medical industries. At first glance, believing that a well-documented standard like ISO 11898 makes it easier to manipulate control functions, whether in an automobile or a medical device such as an MRI or CT scanner, makes sense. This view may be especially true for SAE J1939, the standard for diesel engines, which includes not only trucks but also tanks, ships, trains, and more. The SAE J1939 Standard Collection meticulously documents thousands of parameters (PGNs) transmitted throughout a vehicle network.
The gravity of the security concerns is underscored by real-world incidents. For instance, reports have surfaced about hackers gaining control of modern cars by simply removing the headlights, thereby accessing the vehicle’s control network and enabling them to open the doors and drive away. In another alarming case, hackers successfully disconnected the sway bar in a Jeep Wrangler, a move that could prove catastrophic for the vehicle and its occupants at speeds above 18 mph (29 km/h).
Specifically, in the sway bar scenario, let me be blunt and call this a matter of lousy engineering. Jeep may very well have learned their lesson for newer models - the model in question was a 2010 Jeep Wrangler (AKA Jeep JK) Rubicon 2DR.
But let me address my problem with identifying Controller Area Network as the “enabler” of hacking attempts. Every serial networking technology is vulnerable to “hacking,” specifically ethernet, the basis for the World Wide Web. The point is that networking technology is not the deciding factor for hacking. The motivation for hacking is simple: Because I can. Automobiles and the Internet are desirable targets.
The physical access to a vehicle is not exclusively a CAN weakness. If I wanted to disable a vehicle, I wouldn’t spend weeks or months analyzing and re-engineer CAN data traffic. Multiple, more effective methods exist to immobilize a passenger car or diesel truck. Staying with the CAN technology, I might install a jumper between CAN_H and CAN_L. The result may be unpredictable, but that is exactly what a hacker would have in mind, yet easy to accomplish. A more brutal approach would be stuffing a banana into the exhaust pipe – and yes, I am serious. I'm sure any car enthusiast can generate a list of similarly effective techniques.
The situation becomes more serious when rightful owners or users attempt to add or modify functionality that violates the manufacturer's safety standards. As in the case of the Jeep sway bar, there are serious legal consequences when the access causes damage to the vehicle or drivers and passengers. As previously mentioned, analyzing and re-engineering CAN control functions requires a significant amount of time. However, as the earlier examples indicate, this does not deter dedicated hackers.
However, the primary enabling factor for malicious hacking is remote (non-physical) access. With passenger vehicles, trucks, and even medical devices having experienced a massive increase in connectivity, hackers are more likely to exploit networking vulnerabilities. In particular, wireless networking via WIFI, Bluetooth, or GSM may affect the integrity and availability of connected cars. Consequently, compromised remote access may result in a vulnerable Controller Area Network.
From my perspective, the key to securing a control network lies in meticulous engineering, especially when human lives are at stake. While I won't delve into the specific protection methods in this post, I believe that understanding the various safety aspects and their consequences is a crucial first step. To aid in this, I've compiled a list of informative references below that delve deeper into the topic.
Presentations (YouTube)
Internet References
- ODB-II and the Hacking of Automotive CAN Bus Networks…
- Hack Your Vehicle CAN-BUS With Arduino and Seeed CAN-BUS Shield...
- Car Hacking 101: Practical Guide to Exploiting CAN-Bus using Instrument Cluster Simulator...
Supplement: Truck-to-truck Cyber Worm
The CiA (CAN-in-Automation) introduced this paper in their CAN Community News with the remarks:
"Researchers at Colorado State University have evaluated the risk of attacking the CAN-connectable Electronic Logging Devices (ELD) required by a U.S law. They demonstrate that these devices can be wirelessly controlled to send arbitrary Controller Area Network (CAN) frames, enabling unauthorized control over vehicle systems. The second vulnerability demonstrates that malicious firmware can be uploaded to these ELDs, allowing attackers to arbitrarily manipulate data and vehicle operations. The final vulnerability, and perhaps the most concerning, is the potential for a self-propagating truck-to-truck worm, which takes advantage of the inherent networked nature of these devices. Such an attack could lead to widespread disruptions in commercial fleets, with severe safety and operational implications." Download the paper free of charge.
The primary result of their research is that they have found a vulnerability in the ESP32 processor, specifically in the wireless firmware update (OTA). This proves, yet again, the point of my post: CAN is not the weak link.
SAE J1939 Starter Kit and Network Simulator
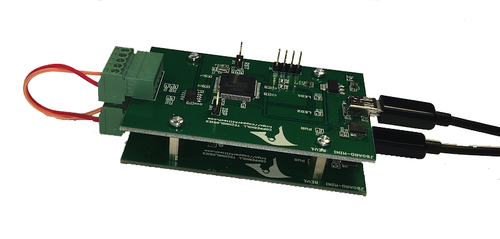
Our SAE J1939 Starter Kit and Network Simulator is designed to allow the experienced engineer and the beginner to experiment with SAE J1939 data communication without the need to connect to a real-world J1939 network, i.e., a diesel engine.
To establish a network, you need at least two nodes, which applies especially to CAN/J1939, where the CAN controller will shut down after transmitting data without receiving a response. Therefore, our jCOM.J1939 Starter Kit and Network Simulator consists of two J1939 nodes, namely our jCOM.J1939.USB, an SAE J1939 ECU Simulator Board with USB Port.
 Loading... Please wait...
Loading... Please wait...