Blog
Recent Posts
SAE J1939, CAN Bus, and Embedded Networking — All in One Place
Posted by on
 If you work with heavy-duty vehicles, mobile machinery, marine systems, or industrial equipment, chances are you have encountered SAE J1939. Whether you are developing embedded firmware, integrating third-party ECUs, or troubleshooting complex vehicle networks, reliable information and robust tools are essential.
If you work with heavy-duty vehicles, mobile machinery, marine systems, or industrial equipment, chances are you have encountered SAE J1939. Whether you are developing embedded firmware, integrating third-party ECUs, or troubleshooting complex vehicle networks, reliable information and robust tools are essential.
That is exactly why we created jcom1939.com.
A Dedicated Platform for J1939 Engineering
JCOM1939.com was designed as a focused, engineering-driven platform built around Copperhill Technologies’ J1939 analyzing and simulation tools — both hardware and software. The core idea is simple: provide practical tools and deep technical knowledge in one centralized resource.
The website is not a generic overview of CAN Bus. Instead, it targets engineers, developers, system integrators, and technical decision-makers who need:
- J1939 monitoring and analysis tools
- J1939 simulation hardware
- Embedded development support
- Protocol-level explanations
- Market and research insights
Copperhill’s analyzers and simulators are positioned as practical development instruments — not just lab accessories. The content reflects that focus by discussing real-world use cases such as ECU testing, network monitoring, protocol validation, and system integration.
Technical Depth Beyond Product Listings
Unlike typical product-focused sites, JCOM1939.com provides substantial educational and reference material. The site includes structured technical discussions on:
- SAE J1939 fundamentals
- PGNs, SPNs, addressing, transport protocols
- Network management and diagnostics
- Implementation considerations in embedded systems
- Interaction with microcontrollers such as Arduino and ESP32
- Bus timing, termination, and physical-layer design
The technical articles move beyond theory and focus on implementation — including monitoring strategies, integration challenges, and troubleshooting considerations. This makes the platform particularly valuable for engineers working on firmware, gateway devices, or diagnostic systems.
J1939-Based Protocols: NMEA 2000 and ISOBUS
The website also addresses J1939-derived and J1939-related standards, including:
- NMEA 2000
- ISOBUS
These protocols reuse or extend J1939 principles for marine and agricultural environments. By covering them alongside core J1939 topics, the site reflects the real-world overlap between heavy-duty, marine, and off-highway systems.
This broader perspective is particularly useful for engineers transitioning between industries or developing cross-domain gateway devices.
CAN Bus Foundations and Emerging Trends
While J1939 is a primary focus, JCOM1939.com also provides foundational CAN Bus coverage. This includes:
- CAN physical layer fundamentals
- Bit timing and arbitration
- Bus loading and topology
- Common design mistakes
- Silent monitoring techniques
- Integration with modern microcontrollers
In addition, the platform addresses industry trends such as the transition toward Automotive Ethernet in advanced vehicle architectures. While CAN and J1939 remain dominant in heavy-duty and off-highway applications, hybrid network architectures are becoming more common. The site acknowledges this evolution and provides context for how J1939 systems fit into broader network ecosystems.
Research Reports and Market Analysis
One of the distinguishing features of JCOM1939.com is its collection of research reports.
These reports cover:
- Technical deep dives into J1939 implementation challenges
- Monitoring and diagnostic strategies
- Market trends in heavy-duty vehicle networking
- Adoption of Automotive Ethernet
- Industry resistance to third-party network access
- Silent-mode monitoring techniques
The reports are written in a structured, engineering-oriented style, aimed at professionals who need both technical clarity and strategic awareness.
Rather than repeating textbook explanations, the research section often explores practical constraints, integration politics, interoperability challenges, and evolving industry architectures.
Bridging Hardware, Software, and Knowledge
The website’s structure reflects its original intention: combine tools and knowledge into a single ecosystem.
Hardware:
J1939 analyzers and simulators for development and validation.
Software:
Monitoring and diagnostic tools designed to work with Copperhill hardware.
Knowledge Base:
In-depth protocol explanations and implementation guidance.
Research:
Market and technical reports to provide broader industry insight.
This layered approach differentiates JCOM1939.com from purely commercial product pages or purely academic protocol references. It is positioned as a working engineer’s resource.
Who Should Visit JCOM1939.com?
The platform is especially relevant for:
- Embedded firmware engineers
- ECU developers
- CAN Bus system integrators
- Agricultural equipment developers
- Marine electronics designers
- Off-highway vehicle engineers
- Technical managers evaluating network tools
If you are developing J1939-based systems or analyzing existing networks, the site provides both the tools and the technical framework needed to move from concept to deployment.
A Focused Engineering Resource
JCOM1939.com was created with a clear mission: support professionals working with SAE J1939 and related technologies through practical tools and in-depth technical insight.
By combining Copperhill Technologies’ hardware solutions with educational content and research reports, the website serves as both a development resource and a knowledge hub.
In a networking landscape that continues to evolve — with CAN, J1939, ISOBUS, NMEA 2000, and Automotive Ethernet coexisting — having a specialized, technically grounded platform is more valuable than ever.
JCOM1939.com is intended to be exactly that.
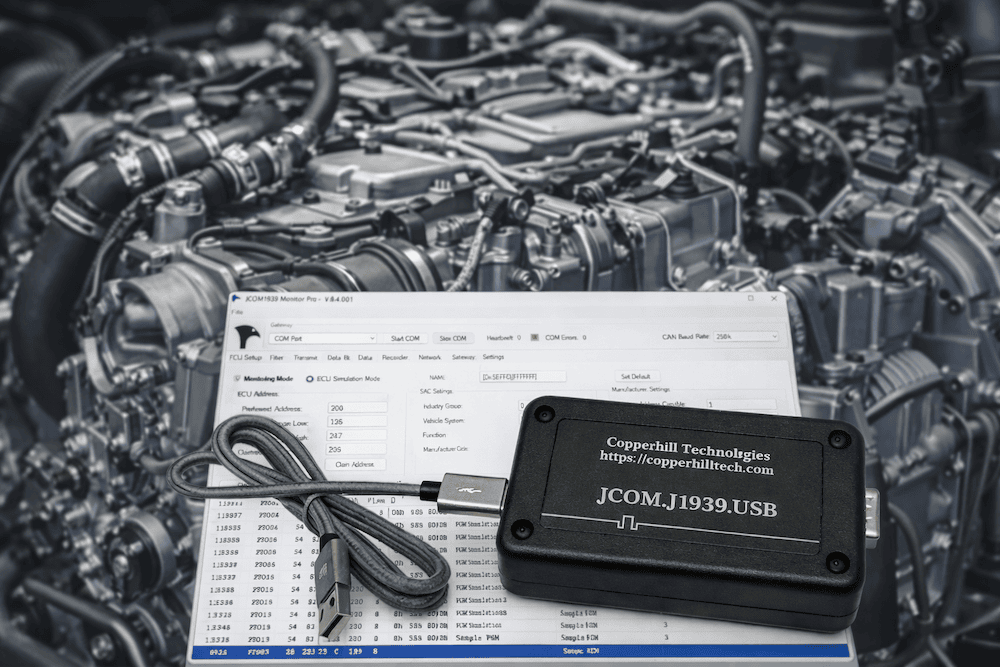
 SAE J1939 to USB Gateway in Plastic Enclosure
SAE J1939 to USB Gateway in Plastic Enclosure
The SAE J1939 to USB Gateway in Plastic Enclosure is a compact, USB-powered interface device that bridges SAE J1939 vehicle networks with standard computing platforms. Built around a fully compliant SAE J1939 ECU simulator board and housed in a rugged plastic case, it enables real-time monitoring, simulation, recording, and analysis of J1939 data traffic directly from any host with a USB COM port. The gateway supports full J1939 protocol functionality including network management and transport protocol, and it comes with free Windows software for packet visualization, message filtering, and ECU simulation, making it ideal for diagnostics, development, and field use.
Designed for ease of integration and robust performance, this gateway presents the vehicle network as a standard COM port to Windows, Linux, embedded systems, and microcontroller platforms. Its durable plastic enclosure protects internal electronics from dust and handling, while features such as programmable filters, automatic node address negotiation, and comprehensive software support simplify tasks from fleet diagnostics to embedded firmware testing. Whether you’re validating network traffic, building custom tools, or simulating ECUs for development and education, this gateway offers a reliable and flexible hardware interface for SAE J1939 applications. More information...
NMEA 2000 Explained: A Practical Guide to CAN Bus Marine Networking
Modern marine electronics rely on NMEA 2000, a standardized CAN-based network that allows engines, sensors, displays, navigation systems, and monitoring devices to communicate over a single, shared backbone. Instead of point-to-point wiring, NMEA 2000 uses a robust two-wire CAN bus to distribute data efficiently and reliably across the vessel. While powerful and flexible, this technology [...]
Why CAN and LIN Need to Communicate in Modern Vehicles
At first glance, it may seem odd that a vehicle would use two different network technologies—CAN (Controller Area Network) and LIN (Local Interconnect Network)—and even stranger that they need to communicate with each other. After all, why not use one network everywhere and avoid the complexity? The truth is that both CAN and LIN exist because [...]
CAN Bus Programming in Python for Automotive, Industrial Automation, and Robotics
The Controller Area Network (CAN bus) is a resilient, lightweight, and efficient communication protocol originally developed by Bosch in the 1980s for in-vehicle networks. It allows multiple microcontrollers (ECUs) and devices to communicate without a central host, using a multi-master, message-oriented design. Over the decades, CAN bus has expanded beyond its automotive roots into domains [...]
Mastering CAN Bus: Essential Guide to Understanding and Troubleshooting Vehicle Networks
In today’s world of connected vehicles and industrial automation, understanding the details of networked communication protocols has become a pivotal skill for engineers and technicians alike. The book Mastering CAN Scratch: Understanding & Troubleshooting (ISBN/ASIN B0G24Z25RZ) steps into this space by offering a comprehensive, hands-on guide to the widely used Controller Area Network (CAN) bus [...]
Mastering CAN Bus: A Deep Dive into Automotive CAN Bus and In-Vehicle Networks
In an age when vehicles are less about purely mechanical linkages and increasingly about interconnected electronics and networks, the book Automotive CAN Bus and In-Vehicle Networks arrives at exactly the right moment. Graham Stoakes presents what he calls “the digital nervous system of modern vehicles” — and for technicians, students, and enthusiasts alike, this translates [...]
Comparing SAE J1939 Baud Rates: Evaluating 250k vs. 500k for Modern Vehicle Networks
For years, SAE J1939 has been synonymous with heavy-duty vehicle networking, and 250k baud has been the de facto standard. But as vehicles grow more connected and data-intensive—think emissions controls, advanced diagnostics, telematics, and electrification—the question arises: is 250k still enough? The recent discussion around adding a 500k baud rate to the J1939 standard aims to [...]
CAN Bus and SAE J1939: A Beginner’s Guide to Network Design
If you’ve ever worked with industrial machines or diesel engines, chances are you’ve heard of CAN bus and SAE J1939. These two go hand-in-hand when it comes to reliable, real-time communication between control units. Let’s break down the essentials of how these networks are designed and why they matter. What Is CAN Bus? CAN (Controller Area Network) [...]
Unlock the Future of Marine Apps with the ESP32-S3 CAN Bus Board with NMEA 2000 Connector
As the marine industry continues to embrace smart technologies, there's a growing demand for powerful, connected, and reliable embedded solutions that can handle everything from engine diagnostics to GPS data aggregation. Whether you're building a marine monitoring system, an onboard data logger, or an intelligent control unit, you need a development board that offers high [...]
Harnessing the Power of the ESP32-S3: A Look at Copperhill’s CAN FD Development Board
In the evolving landscape of IoT, industrial automation, and automotive communication, the demand for a versatile, wireless-enabled microcontroller with CAN bus capabilities has never been greater. Copperhill Technologies rises to the occasion with its latest innovation—a development board based on the ESP32-S3-WROOM-1-N8R8, engineered to support both Classical CAN and CAN FD protocols. At the heart of [...]
 Loading... Please wait...
Loading... Please wait...
