Blog
Recent Posts
OBD-II and the Hacking of Automotive CAN Bus Networks
Posted by on

Let me clarify: this is not a guide to hacking automotive networks. Instead, I attempt to dismiss some common misconceptions about OBD-II and its supposed ability to control a vehicle (Spoiler alert: It cannot). As someone who has spent considerable time studying and working with CAN Bus technologies, I think it is time to set the record straight.
When I first contemplated writing this post, I was tempted to title it 'And nobody understands OBD-II.' I was once part of that group of unknowing buffs, and I chose to remain ignorant to avoid a fiercely competitive and over-saturated market. However, the flood of inquiries I received, ranging from the crazy to the interesting, prompted me to reconsider. The common perception was that they had to connect to the onboard OBD-II port, monitor, and analyze CAN Bus data traffic, and insert the control commands according to the envisioned application.
It became clear that many were unaware of the wealth of documentation available on OBD-II, a fact that I found both surprising and, I admit, slightly amusing. After all, most of their questions could have been answered by a simple read through the appropriate documentation, saving us valuable time and effort.
What is OBD?
Let's get to the point: OBD-II, which stands for On-Board Diagnostic Version 2, is a standardized system that allows external electronics to interface with a car’s computer system. It's not about control but about diagnosis. As vehicles have become increasingly computerized, OBD-II has become more critical, with software playing a pivotal role in fixing many problems and unlocking performance.
The point is that OBD is On-Board Diagnostic, not On-Board Control. OBD provides data that reports engine performance and status. Inserting data into the OBD port does not impact any vehicle functionality.
Investigating a Vehicle CAN Bus
The question arises: with OBD-II unsuitable for hacking, where does vehicle control occur? The simple, widely overseen fact is that vehicles have multiple (at minimum two) CAN Bus networks, one for OBD-II, the other(s) for various control functions. The tricky part is to identify the network(s) and find access points.
If you try to get information on how many networks a vehicle uses and what control functions it includes, you will run into a roadblock. That information is highly proprietary and changes from manufacturer to manufacturer and even from one vehicle series to the other.
Modern cars are becoming increasingly computerized with infotainment and navigation systems, Wi-Fi, and automatic software updates. These innovations aim to make driving more convenient for drivers. However, it is alarming that vehicle technologies have not kept pace with the current hostile security environment, leaving millions of drivers vulnerable to attacks.
To address this issue, The Car Hacker’s Handbook provides a comprehensive guide to understanding modern vehicles' computer systems and embedded software. The handbook provides an overview of vulnerabilities in the vehicle's communication network and detailed explanations of communications via the CAN bus and between devices and systems.
Once you have a good understanding of a vehicle’s communication network, the handbook will teach you how to intercept data and perform specific hacks such as tracking vehicles, unlocking doors, glitching engines, flooding communication, and much more. The Car Hacker's Handbook is an essential guide that equips drivers with the technical knowledge to defend against any potential cyber-attacks. More Information...
The Hacking Aspect
For argument’s sake, if you plan to carry out a malicious attack on a vehicle's anti-block system or brakes, you need to be aware of the potential legal consequences and the amount of effort and time it may take to collect and apply the necessary data. Additionally, you would require physical access to the targeted vehicle, which should not be taken lightly. It is crucial to note that attempting such attacks is both illegal and dangerous, and doing so can result in severe consequences.
The main point is that despite the possibility of hacking, it is not a practical or useful activity. Simply put, it is a waste of time, although this argument may not dissuade some people. The only potential use I would consider is to test the network's resilience by attempting to crash it and then report the results to the manufacturer and public. I strongly believe that CAN Bus networks can be easily disrupted and rendered inoperable.
However, with passenger vehicles having experienced a massive increase in connectivity, hackers are more likely to exploit vulnerabilities in wireless networking, Bluetooth, and GSM to affect connected cars' confidentiality, integrity, and availability. This will allow non-physical, i.e., remote access.
Field manual on contextualizing cyber threats, vulnerabilities, and risks to connected cars through penetration testing and risk assessment.
Hacking Connected Cars deconstructs the tactics, techniques, and procedures (TTPs) used to hack into connected cars and autonomous vehicles to help you identify and mitigate vulnerabilities affecting cyber-physical vehicles.
Written by a veteran of risk management and penetration testing of IoT devices and connected cars, this book provides a detailed account of how to perform penetration testing, threat modeling, and risk assessments of telematics control units and infotainment systems.
This book demonstrates how vulnerabilities in wireless networking, Bluetooth, and GSM can be exploited to affect confidentiality, integrity, and availability of connected cars. More Information...
The Liability Aspect
For obvious reasons, vehicle manufacturers would prefer that you do not pamper with their vehicle control functions. As I mentioned previously, you need to be aware of the potential legal consequences when your access causes damage to the vehicle or drivers and passengers. However, that does not mean that these manufacturers designed their networks to the highest safety standards.
I found an article where the hacker explained how to disconnect the sway bar on a 2010 Jeep Wrangler (AKA Jeep JK) Rubicon 2DR by accessing the CAN Bus. A sway bar, also known as an anti-sway bar or anti-roll bar, is a component of some vehicles’ suspensions. Its purpose is to reduce roll and sway during cornering and other maneuvers. While researching the sway bar function, I also found a video by Jeep referring to the sway bar. They also posted a warning message: “Do not disconnect the sway bar and drive on hard-surfaced roads or at speeds above 18 mph (29 km/h), or you could lose control of the vehicle, which can result in serious injury.”
Source: Electronic Front Sway Bar Disconnect | How To | 2020 Jeep Wrangler...
Regarding your OBD-II Application
I always emphasize that professional engineering begins with conducting thorough research, which involves extensive reading. Though the process may seem tedious and time-consuming, there are no shortcuts. If you have a groundbreaking idea involving vehicle networks, take your time to investigate the technology carefully.
See also my post Know OBD2 Before You Start That Development Project...
More Resources
- Hack Your Vehicle CAN-BUS With Arduino and Seeed CAN-BUS Shield...
- Car Hacking 101: Practical Guide to Exploiting CAN-Bus using Instrument Cluster Simulator...
Disclaimer
This post is based solely on publicly available information and logical deduction. I have not disclosed any confidential or proprietary data. However, errors are always possible. Therefore, if you have any additional information or wish to demonstrate that I am mistaken, please do not hesitate to contact us through our " Contact Us" page.
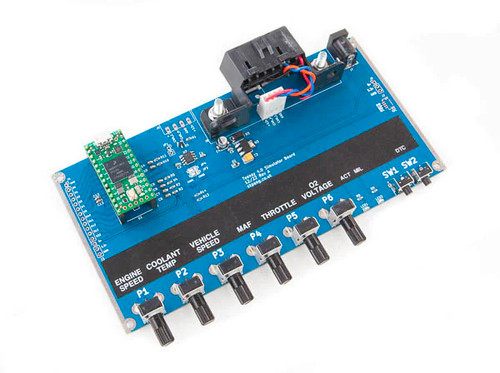
Teensy 4.0 OBDII CAN-Bus ECU Simulator Includes Teensy 4.0
This is a CAN-Bus OBDII ECU simulator using the Teensy 4.0 module (included). Useful for testing OBDII interface and writing diagnostic software. ECU PIDs parameters are adjustable via potentiometers. Most programs written for Arduino work on Teensy. All of the standard Arduino functions (digitalWrite, pinMode, analogRead, etc) all work on Teensy. Teensy has the same built-in peripherals as the Arduino: analog inputs, SPI, I2C, PWM, and a real serial port. This board requires a 12 VDC power supply. A 12 VDC adapter is included. More Information...
 Loading... Please wait...
Loading... Please wait...