Recent Posts
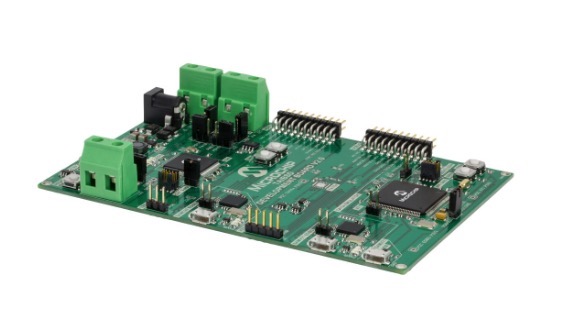
In-Vehicle Security Development Kit With CAN Bus And CAN FD Message Authentication
Posted by on
Microchip Technology introduced their CryptoAutomotive In-Vehicle Network (IVN) TrustAnchor/Border Security Device (TA/BSD) development kit. This kit is designed to enable OEMs and Tier 1 suppliers to introduce security to networked vehicle systems, starting in areas of priority, without disruption elsewhere. The CryptoAutomotive TA/BSD development kit emulates a secure node in an automotive network and provides system designers with a starting point for implementing security. Designed to be flexible, the tool accommodates each OEM’s implementation by allowing manufacturers to configure the node to conform to various specifications and industry standards. The tool demonstrates secure key storage, Electronic Control Unit (ECU) authentication, hardware-based crypto accelerators and other cryptographic elements. When used with a host microcontroller, it enables designers to implement functions such as secure boot and Controller Area Network (CAN) message authentication, including conversion of CAN 2.0 messages to CAN Flexible Data Rate (CAN-FD) with appended Message Authentication Codes (MAC) when appropriate.
With the companion approach, the TA/BSD emulation kit enables OEMs to continue using their existing microcontrollers (MCUs) and existing MCU firmware certified to required safety standards by later adding the companion chip the kit emulates. These companion chips will come to the customer preprogrammed and include built-in security measures to provide true hardware-based key protection. This can entail re-architecture of the MCU firmware to implement secure zones with hardware and software domains.
The tool can be used with any ECU, architecture, configuration or bus, providing the flexibility to implement security in existing systems without large-scale redesigns. The companion chip solution requires minimal MCU code updates. This approach also removes the requirement for in-house security expertise. The tool provides an online Graphical User Interface (GUI) program with pre-configured options to simplify and facilitate implementation.
 When the Controller Area Network (CAN) was designed, security was not a requirement. The primary usage of CAN was considered closed; possible intruders or attackers would simply not get physical or remote access to the network.
When the Controller Area Network (CAN) was designed, security was not a requirement. The primary usage of CAN was considered closed; possible intruders or attackers would simply not get physical or remote access to the network.
However, today it is more and more common that devices connected to a CAN system also have connections to other networks, including the Internet.
Recent car hacks have shown that attackers may get access to CAN systems. Without strong security features, an attacker automatically gains full access to everything connected, allowing active control commands to be recorded and replayed.
In this book we examine which options developers of CAN based systems realistically can use to provide adequate security features.
- What can we do - without using heavy-weight security features?
- What can we do - to detect possibly injected messages?
- What can we do - without any hardware change? What can we do - with minimal software change?
The CANcrypt protocol and software is introduced as a scalable security solution for the Controller Area Network.
 Loading... Please wait...
Loading... Please wait...